Escape Room
Students will create and program their own escape room security system.
Questions to investigate
• How can conditions be set to create a secure “room” to break out of?
Prepare
• Ensure SPIKE Prime hubs are charged, especially if connecting through Bluetooth.
Engage
(Group Discussion, 15 minutes)
Engage students in a conversation about escape rooms.
Ask students if they have ever participated in or heard of a breakout or escape room. Consider showing images or videos to students. Explain that in these games participants use clues and complete puzzles to figure out how to get out of the locked room.
Brainstorm
Brainstorm different ideas of puzzles that could be used in an escape room.
As a group, brainstorm several ideas for creating a secure device that could be used in a breakout or escape room.
Ask students to then work in their smaller groups to create a short survey to ask other students what they would like in a security system or something to break out of. Students can share examples they are thinking about using and ask for other ideas. Students should include 3 questions about what would be fun, challenging, and ideas of themes. Students want to ensure the user interest in their escape device and also age-appropriateness of the idea.
Allow students time to create and complete their survey.
Explore
(Small Groups, 45 minutes)
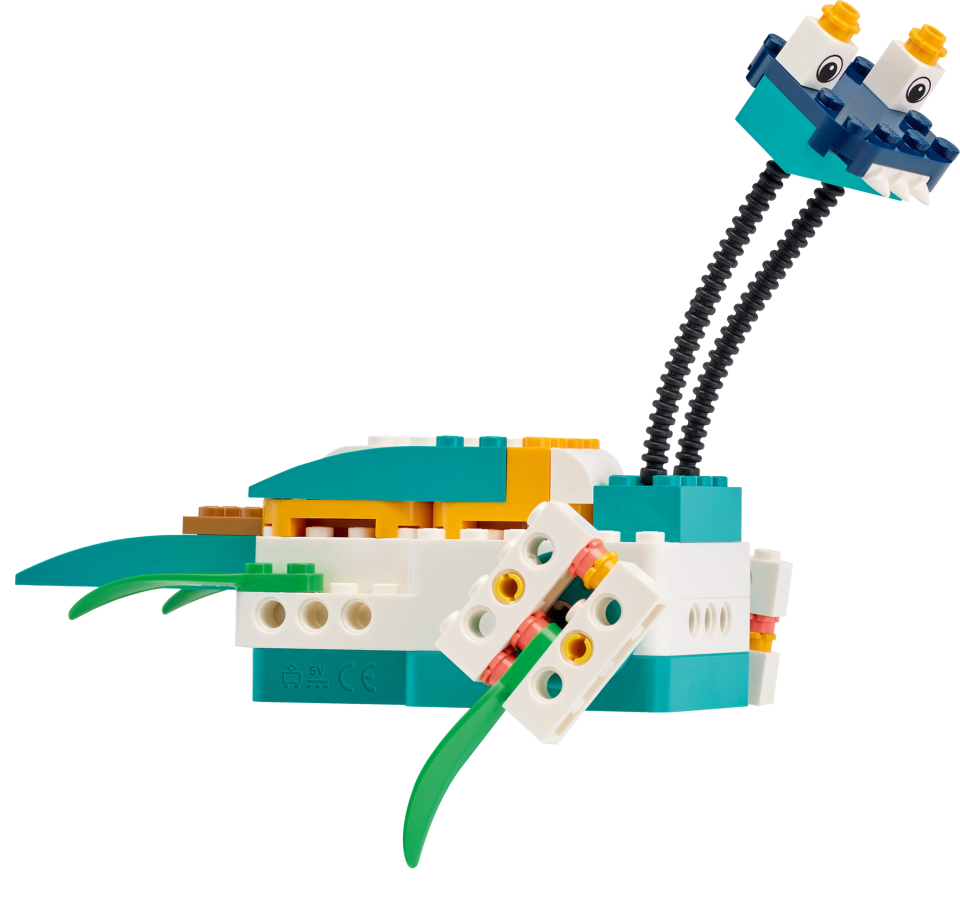
Students will design, build, and program a puzzle game to use in an escape room.
Design and Choose the Right Idea
Students should consider the input from their surveys and start to design their security device that will be used in a breakout room.
Students will design, build, and program a device that could be used in a breakout or escape room. The constraints are:
1. It must use the light matrix
2. It must use at least one motor
3. It must use at least one sensor
4. It must include a logic operator in the program
5. It must include at least two steps to crack the code.
Students should create a sketch of their building idea and a flowchart of their programming idea.
Test and Iterate
Allow time for students to test and analyze their ideas as they go, making improvements where needed. Students should test and evaluate their designs against the design criteria set and their flowcharts as they start making their solutions.
Ensure students use sketches and photos of their models to record in their design journey.
Allow students to receive feedback on their designs as time allows. This can be from other groups or the teacher.
Explain
(Whole Group, 15 minutes)
Students should share their design and explain how it works. Conduct an initial sharing session with students.
Ask students questions like:
• How did you program your model to create a security device with at least two steps? Ask students to share their program comments to explain.
• What decisions did you have to make while creating your design?
• What type of conditional statement did you choose?
• What were areas that you had to debug or troubleshoot?
• What was difficult about this challenge?
Elaborate
(Small Groups, 25 minutes)
Allow students additional time to complete their program after the initial sharing session.
Students should finalize their design and program. Encourage students to incorporate any new ideas they get from the sharing session.
Leave the models together if you are completing the lesson on feedback next.
Evaluate
(Group Exercise, 10 minutes)
Teacher Observation:
Discuss the program with students.
Ask students questions like:
• What was difficult about this challenge?
• What was your approach to solving this challenge?
• What type of logic operators did you include and why?
Self-Assessment:
Have students answer the following in their journals:
• What did you learn today about creating your own design based on given criteria?
• What characteristics of a good teammate did I display today?
• Ask students to rate themselves on a scale of 1-3, on their time management today.
• Ask students to rate themselves on a scale of 1-3, on their materials (parts) management today.
Teacher Support
Students will:
• Create a security device to simulate a break out game
• Design a device that meets given constraints
• SPIKE Prime sets ready for student use
• Devices with the SPIKE App installed
• Student journals
CSTA
2-CS-02 Design projects that combine hardware and software components to collect and exchange data.
2-AP-10 Use flowcharts and/or pseudocode to address complex problems as algorithms
2-AP-13 Decompose problems and subproblems into parts to facilitate the design, implementation, and review of programs.
2-AP-16 Incorporate existing code, media, and libraries into original programs, and give attribution.
2-AP-17 Systematically test and refine programs using a range of test cases.
2-AP-19 Document programs in order to make them easier to follow, test, and debug.
2-IC-22 Collaborate with many contributors through strategies such as crowdsourcing or surveys when creating a computational artifact.